Single Node Openshift running on OCP-V disconnected
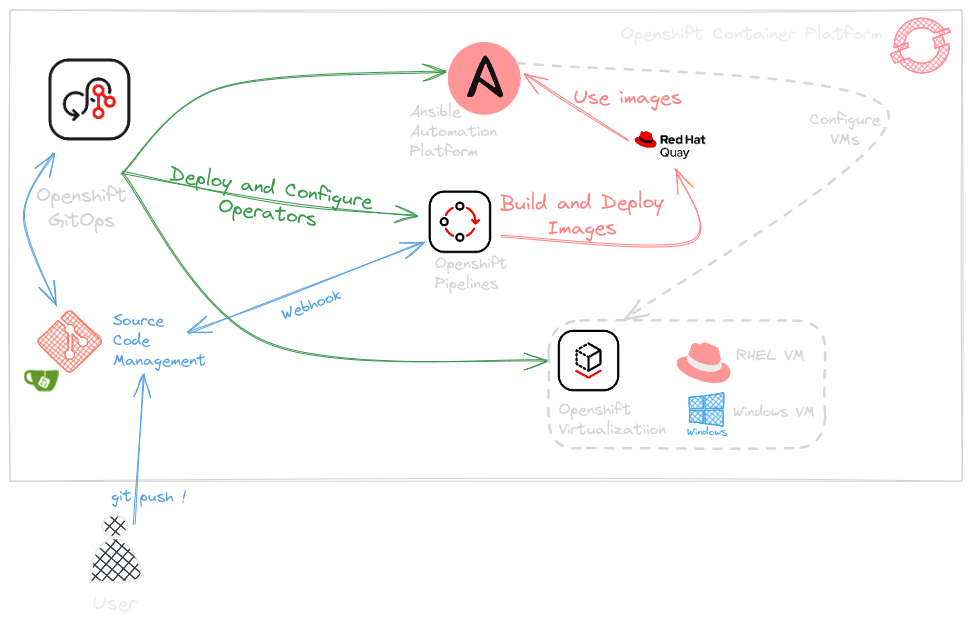
LAB overview
In this LAB, I’m going to deploy a single node OpenShift Cluster in Openshift Virtualization using a private network without internet access.
1. Requirements
A linux machine with clients installed
- Openshift Client https://mirror.openshift.com/pub/openshift-v4/x86_64/clients/ocp/stable/openshift-client-linux.tar.gz
- Openshift install client https://mirror.openshift.com/pub/openshift-v4/x86_64/clients/ocp/4.17.16/openshift-install-linux.tar.gz
- oc mirror https://mirror.openshift.com/pub/openshift-v4/x86_64/clients/ocp/latest/oc-mirror.rhel9.tar.gz
- virtctl (Get the downlond links from the Openshift Console)
A mirror registry to store Openshift Images Mirror registry for Red Hat openshift will be used in this lab